Extensive Sensitive Data Manipulation
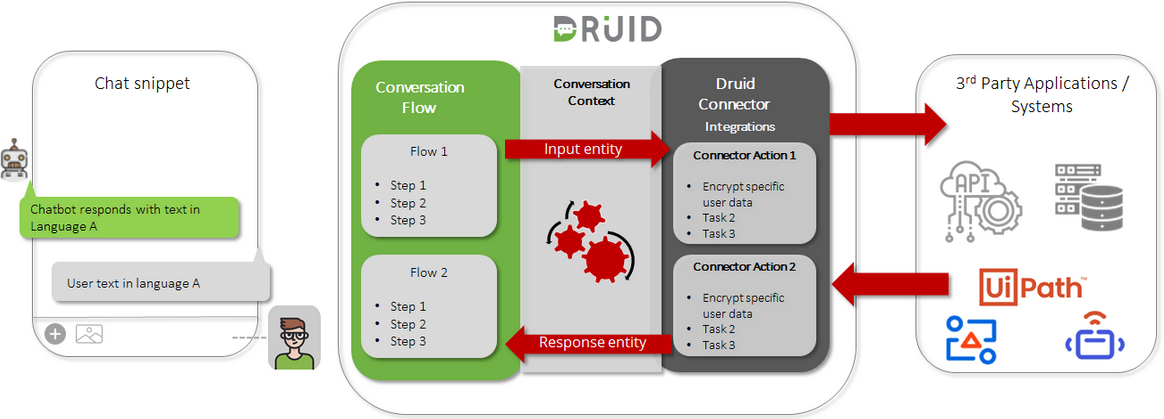
DRUID provides bot authors with extensive options to create chatbots able to securely capture sensitive data from chat users (passwords, credit card numbers, etc.) / receive secure data from external systems and transfer it in an encrypted way to third party applications using connector integrations.
This section describes how you can author the chatbot so that you address data encryption on different layers throughout a conversation.
Capturing sensitive data securely
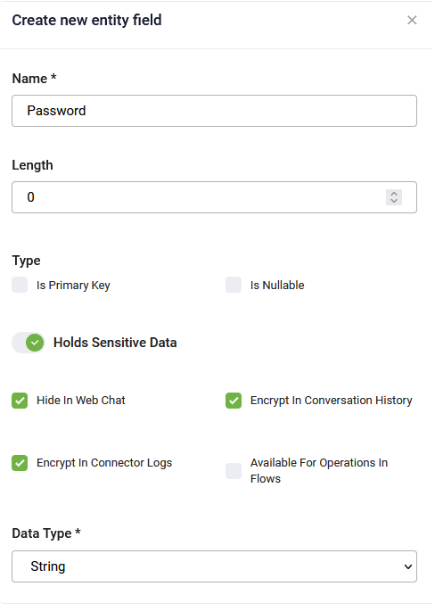
To securely capture user sensitive data / receive sensitive data from external systems, in Input Mapping on prompt steps, use fields which have Holds Sensitive Data selected.
By default, the maximum security configuration for sensitive data manipulation. In default configuration, DRUID masks the sensitive data in the web chat (the value provided by the user and sent by the bot to the user), in the conversation history (including Chat Activity Data) and in connector logs. You can select the configuration that suits your needs best. For more information on how to configure the entity fields that will store sensitive data and the different configurations available, see Manipulate Sensitive Data.
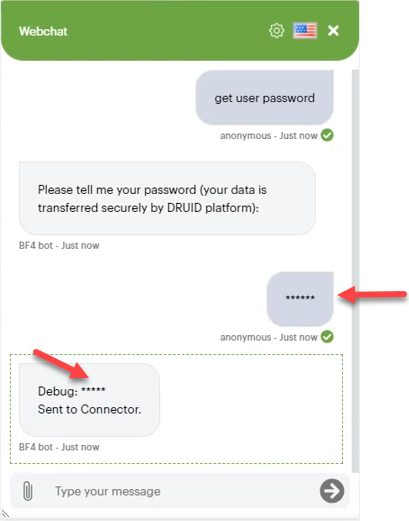
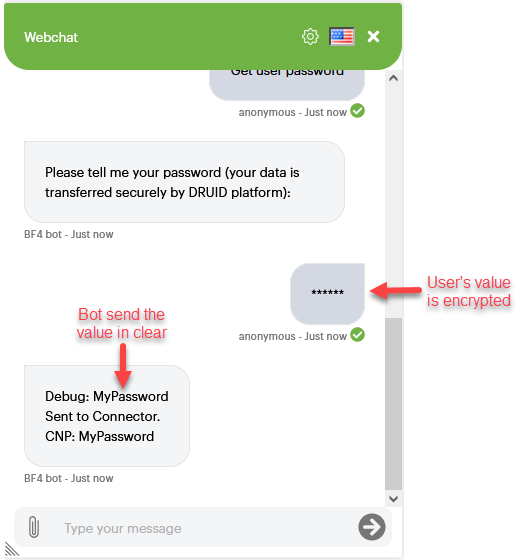
The figure below provides a prompt step example where the user is asked to provide the password (that is, sensitive data).
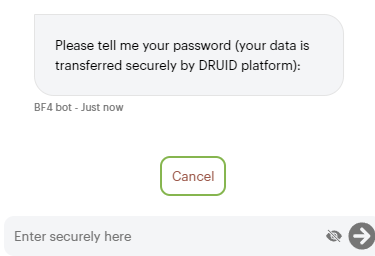
Whenever a prompt step that will store sensitive data is executed, the Cancel button is automatically displayed in the chat giving the user the possibility to continue the conversation without proving the requested sensitive data.
If the user clicks the Cancel button, the following string is stored in the entity field specified in Input mapping on the prompt step: “UserCanceledInput”. You can use this value at authoring time to provide alternative conversation paths.
The user data will be encrypted using a DRUID proprietary encryption method from the moment the user inputs data in the chat and remains encrypted while being transmitted to the connector. The connector will decrypt the data using a DRUID proprietary decryption method and send the data to external systems (if data encryption is not set on connectors).
When a bot deployed in the MS Teams channel asks the user to enter sensitive data, it has a channel-specific behavior. For more information, see Prompt Steps Configuration.
Manipulate Sensitive Data
Druid offers robust options for managing sensitive data within entity fields, ensuring maximum security and compliance. By effectively managing entity fields and sensitive data, you can optimize your AI Agent functionality while upholding stringent security standards.
Enable the Holds Sensitive Data option to encrypt user data using proprietary encryption methods.
Regardless which configuration you use for sensitive data manipulation, Druid always encrypts the data using a proprietary encryption method from the moment the user inputs data in the chat and remains encrypted while being transmitted to the connector. The connector will decrypt the data using a Druid proprietary decryption method and send the data to external systems.
Hide In Web Chat
Druid masks in the web chat both the value provided by the user, and the one sent by the AI Agent to the user.
Encrypt In Conversation History
Druid encrypts the value provided by the user in the Conversation History database and in the Chat Activity Data.
Encrypt In Connector Logs
Druid encrypts the value provided by the user in the Connector logs.
Available For Operations In Flows
You can use the user’s value during the conversation flow runtime, to manipulate the context data stored in sensitive fields: alter the data, perform RegEx validation, calculations, show the information in a message, etc.).
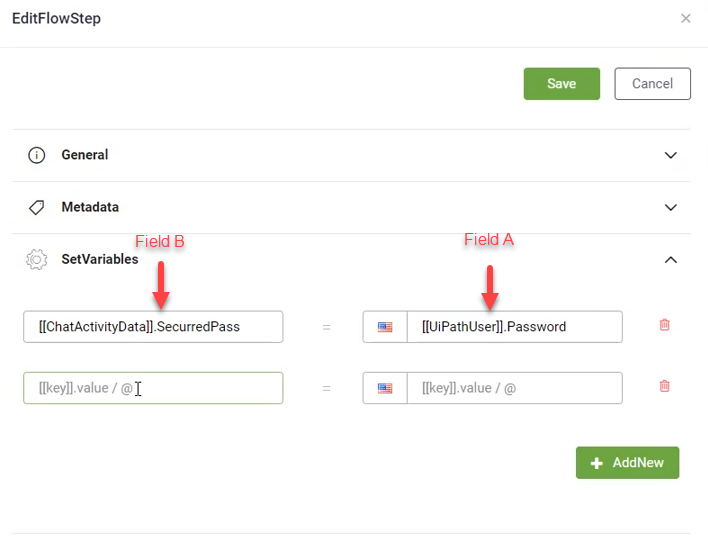
When working with Set variables, authors must assure that, when moving values form one entity field to another, both entity fields involved have IDENTICAL sensitive data configuration (“Available for operations in flows” attribute is the same for both entity fields).
The table below provides the allow manipulation matrix of the two fields used in Set Variables.
| Field A – Available for operations = TRUE | Field A – Available for operations = FALSE | |
| Field B – Available for operations = TRUE | same encrypted value | double encrypted |
| Field B – Available for operations = FALSE | same encrypted value | same encrypted value |
| Field B does not hold sensitive data | data in clear | same encrypted value |
Transmitting sensitive data to third party applications in a secure way
DRUID enables bot authors to address the cases when third party applications require that specific user information is transmitted in a secure way to ensure that unauthorized parties do not tamper or spoof the data.
Bot authors can now achieve this by designing their chatbots to encrypt the data transmitted by DRUID connectors using the AES GCM encryption algorithm.
Constructed from the Advanced Encryption Standard (AES) algorithm with a block size of 128 bits, AES with Galois/Counter Mode (AES-GCM), a state of the art encryption algorithm, that is a block cipher mode of operation that provides high speed of authenticated encryption and data integrity.
To achieve data transmission to third party systems in a secure way, follow these two steps:
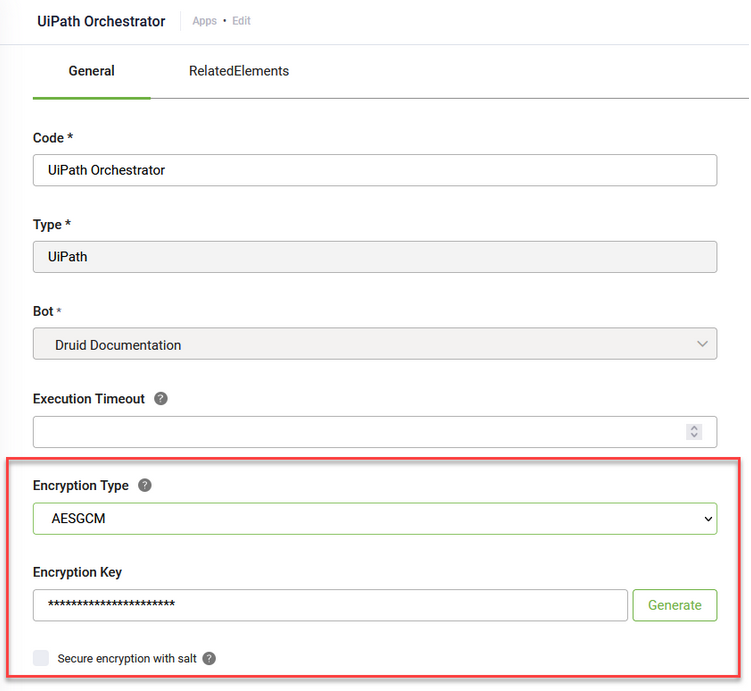
Step 1. Set data encryption when defining the connection strings (app)
On the connector app, select the encryption type AES CGM and generate an encryption key.
If you want to encrypt the data with a higher level of security, on connector apps, select Secure encryption with salt. By doing so, DRUID will alter the DRUID fields with a random 64-bit salt and then will encrypt the data using the AES CGM algorithm and the encryption key from the connector app specified in the Encrypt Data integration task.
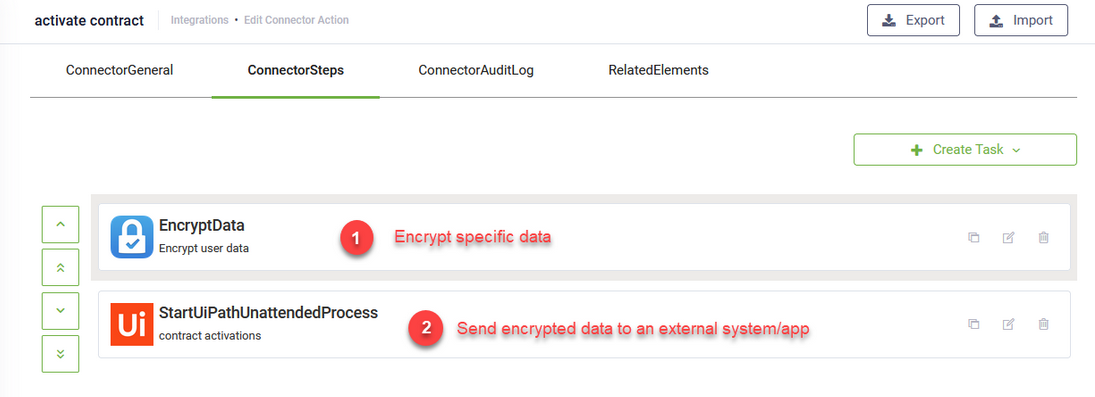
Step 2. Use the Encrypt Data integration task
Use Encrypt Data as the first integration task on all connector actions (if needed) to encrypt user data stored in specific DRUID entity fields (fields from the request entity set on the connector action), and store the encrypted data temporarily at runtime during the execution of the integration tasks within that connector action.
When defining the connector actions, you first encrypt the data based on your needs by using the Encrypt Data integration task, and then use that data on subsequent tasks.
If you want to add data encryption on existing connector actions, add the Encrypt Data task, configure it and then use the drag and drop functionality to make it the first integration task to be executed in that connector action.
For more information on the Encrypt Data integration task and how clients receiving the encrypted data can decrypt it, see Encrypt Data.